Two Holes In The Ivanti Fence: The Wolves Were Already Inside
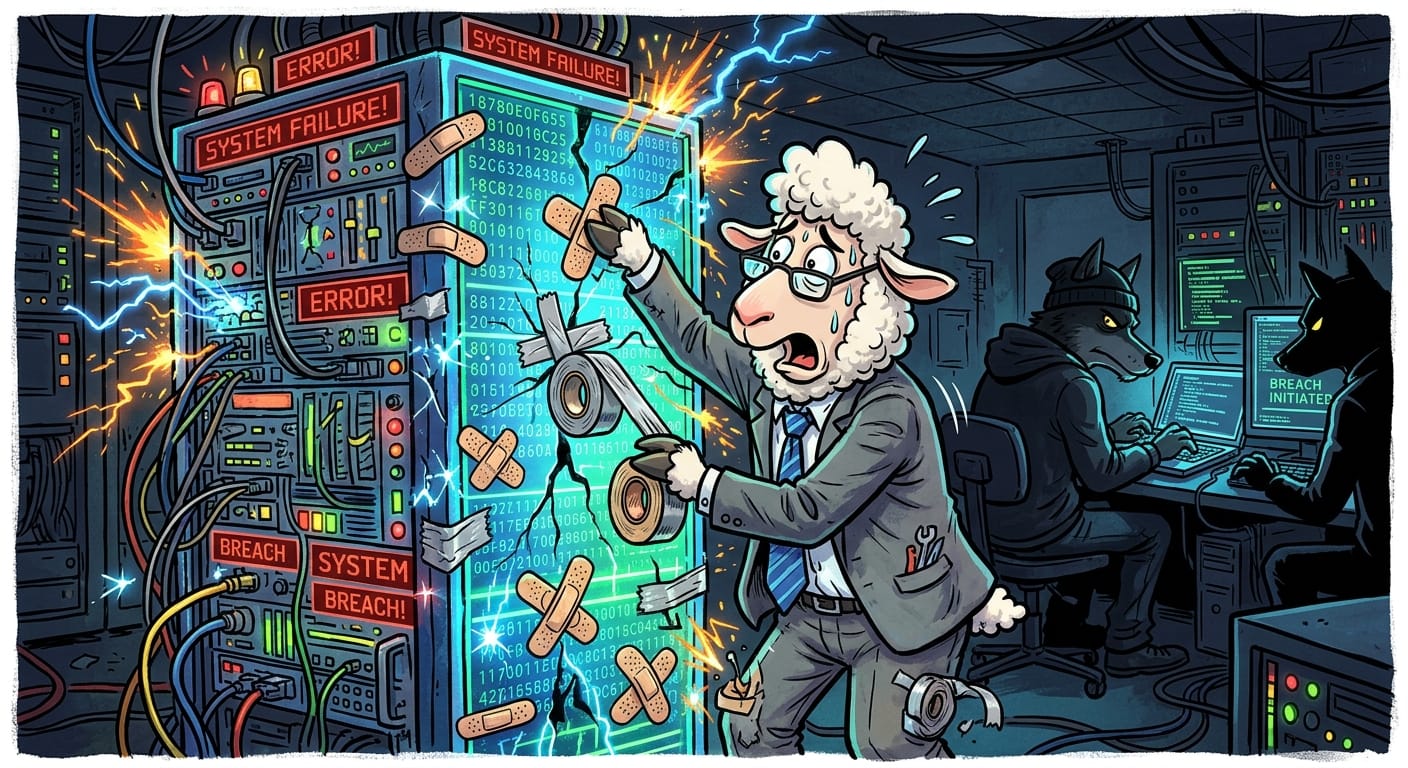
I am going to say something that will surprise absolutely no one who has attended my quarterly threat briefings: remote code execution via an unpatched mobile device management platform is not a sophisticated attack. It is a failure of basic perimeter discipline. It is leaving the gate open and then acting bewildered when you find wolf tracks near the hay.
Ivanti's EPMM product, which manages the mobile endpoints of your flock, was found to contain not one but two holes in the fence simultaneously. CVE-2026-1281 has already earned itself a spot on CISA's Known Exploited Vulnerabilities catalog, which is the government's formal way of saying "the wolves have already been through here, please look at your sheep."
Versions prior to 12.8 are affected. CISA does not add things to that list as a precaution. They add them because active exploitation is confirmed. The wolves were not casing the property. They were already inside, helping themselves.
The Sky Pasture integration angle here is particularly troubling. Mobile device management platforms are the crook of the shepherd's staff. If a wolf controls that, it controls the entire flock's movement. Remote code execution means the attacker is not knocking. They are already seated at your desk, drinking your coffee, and forwarding your files.
In the old days, we managed endpoints with magnetic tape logs and physical access controls. You knew who touched the terminal because there was a sign-in sheet bolted to the wall. Now we have sprawling Sky Pasture MDM consoles with internet-facing portals and the Shepherds wonder why the lambs keep getting sheared by outsiders.
I have no sympathy. I have only recommendations.
Remediation
Apply the ointment immediately. Upgrade to EPMM version 12.8 or later. Ivanti has released the patches. There is no excuse for delay. None. I do not want to hear about change management windows.
Audit your exposure. If your EPMM portal is internet-facing with no additional access controls around it, you have built a very attractive gate for the wolves. Restrict access. Put it behind a Sheep Tunnel at minimum.
Check for signs of prior intrusion. Because CISA confirmed active exploitation, assume the wolves may have already visited. Review your logs for anomalous API calls and unauthorized configuration changes before and after the vulnerability disclosure window.
Tell the Shepherds. Yes, they will not understand it. Tell them anyway. Frame it as a financial risk. That is the only language that reliably reaches that particular pasture.
The fence has been repaired. Whether you were already compromised before the ointment arrived is the question that should be keeping you awake tonight.
Woolridge out. Go patch something.
Original Report: https://thehackernews.com/2026/01/two-ivanti-epmm-zero-day-rce-flaws.html
