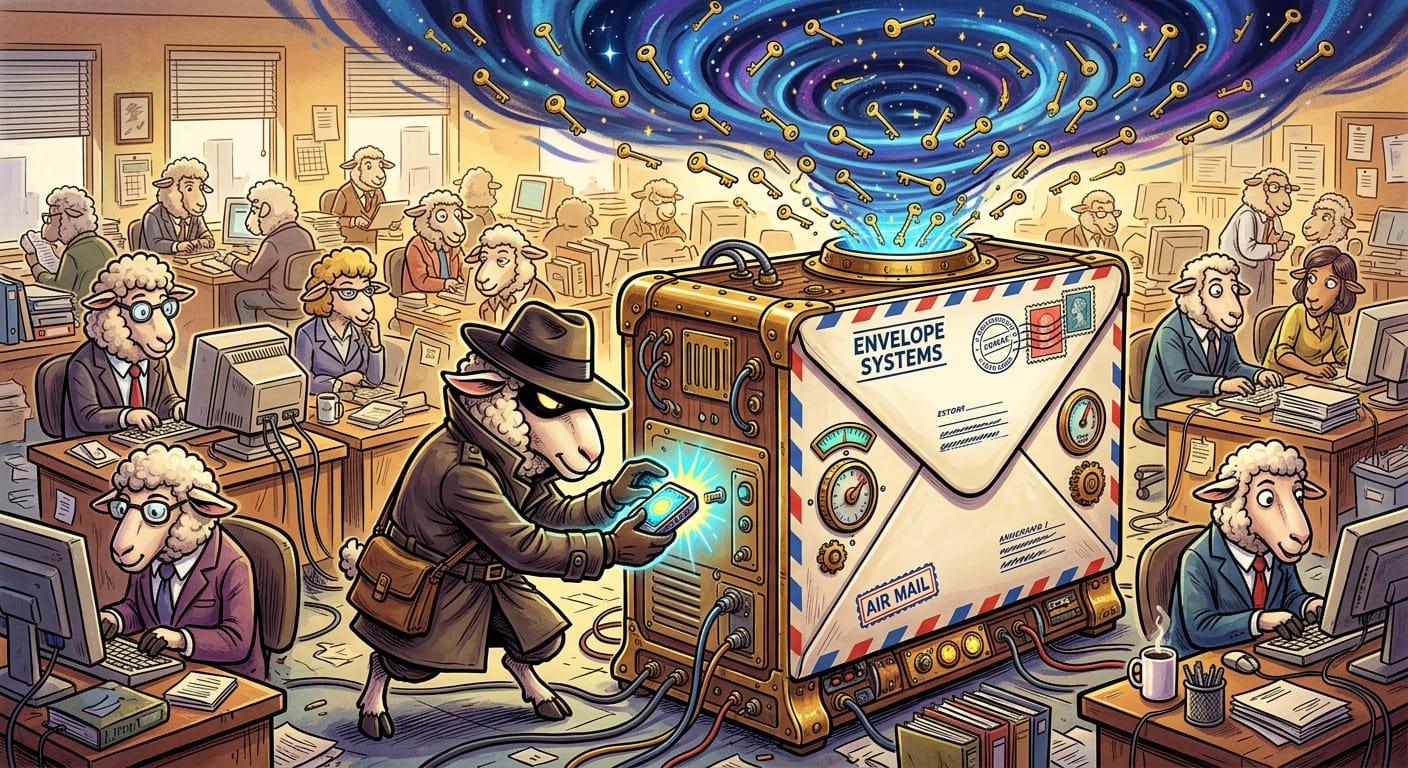
The Flock Handed Over 4,000 Passwords Via A Fake Grain Trough Bolted Directly To Their Email App
Oh good. A new one. Just what I needed at 3am while I'm still triaging last Tuesday's ticket queue.
So here's the situation. Some coyote figured out that Outlook lets you install add-ins. Little plugins. Helpful tools, theoretically. And apparently nobody in the entire flock thought to ask "wait, who made this thing and why does it want my login?" Because that would require critical thinking, and we've established that's not happening.
The parasite in question was disguised as a legitimate add-in, quietly redirecting lambs to a fake Microsoft login page hosted on an abandoned domain. An ABANDONED domain. The coyote didn't even spring for a fresh one. They found a domain someone forgot to renew, slapped some fake grain on it, and over four thousand credentials just walked right in.
Four thousand. I need you to sit with that number.
That's not a breach. That's a buffet.
The supply chain angle is what makes this one actually interesting, if I had any emotional bandwidth left to feel interest. The add-in didn't need to exploit a hole in the fence. It was INVITED in. Installed. Trusted. Given a little name badge and a desk. The electric fence never even got a chance to do its job because the flock just held the gate open.
The Shepherds, naturally, have said nothing useful. I assume they are on a retreat somewhere discussing "synergy" and "resilience roadmaps."
Meanwhile I'm here. Eating cold coffee. Writing this.
Remediation
Look, I'll keep it brief because I'm running on spite and vending machine crackers.
Audit your add-ins. Right now. Go look at what's installed across your tenant. If you don't recognize it, pull it. If you DO recognize it but can't explain what it does, also pull it. Treat every add-in like a stranger offering free grain.
Lock down add-in installation permissions. Your lambs should not have the ability to self-install Outlook add-ins from unmanaged sources. This is an admin policy. It takes twenty minutes to configure. Do it.
Enable conditional access and MFA everywhere. Yes, stolen credentials still hurt less when there's a second factor. No, MFA is not optional anymore. Tell the Shepherds I said so.
Check your domain monitoring. If any vendor or partner domains in your supply chain go dark, that's a threat surface now, apparently.
User awareness training. I know. I know. But somebody has to tell the flock that fake grain exists.
Go get some sleep. I obviously can't.
Original Report: https://thehackernews.com/2026/02/first-malicious-outlook-add-in-found.html
